Understanding the Critical Role of a VPN in Modern Digital Life
In an era where digital vulnerabilities are escalating, safeguarding your personal information has never been more essential. A VPN encrypts your internet traffic, ensuring that cybercriminals, internet service providers, and external entities cannot monitor your browsing habits. Whether you’re using public Wi-Fi at a coffee shop or processing confidential files, a VPN acts as an invisible barrier against information theft.
Many users overlook the risks of unprotected hotspots, leaving vulnerable their credit card numbers, passwords, and communication logs. By redirecting your connection through encrypted servers, a 快连官网 masks your digital location and physical whereabouts, making it extremely difficult for data collectors to identify you.
Selecting the Ideal VPN for Your System: A Comprehensive Comparison
Choosing the right VPN service depends on your unique requirements and platform. For Microsoft enthusiasts, look for intuitive designs, fast servers, and military-grade protection. Mac users should prioritize smooth compatibility with Handoff features, while Linux aficionados may favor configurable options.
Smartphone users must opt for VPNs with compact software that minimize battery drain and network load. Universal access is essential if you regularly move between laptops, tablets, and handsets. Always verify that your VPN accommodates modern standards like IKEv2 for peak efficiency.
Step-by-Step Guide to Setting Up a VPN on Windows
First, navigate to the provider’s portal using a reliable browser. Identify the installation page and select the PC-friendly edition. After acquiring the file, launch the setup file and adhere to the installation wizard.
During setup, customize options like automatic startup and security method. Turn on the emergency stop feature to block breaches if the VPN loses signal. To conclude, log in with your username and password and link to a server of your choice.
Optimizing VPN Usage on Mac Systems
MacOS delivers built-in compatibility for VPNs, but specialized tools often offer better functionality. Post-installation, drag the VPN application to your program directory. Open the app and input your login data to initiate the service.
Modify configurations such as encryption standards and node choices. Turn on selective routing to route certain programs through the 快连电脑版 while letting others to use your standard internet. For added protection, combine your VPN with privacy apps to stop spyware and scam websites.
Securing Open-Source Platforms with a VPN
Tech enthusiasts often favor VPNs that support scriptable configurations. First, updating your system library to confirm access to the most recent tools. Use terminal commands to deploy the VPN application, abiding by guides provided by your service.
Adjust system preferences to automate VPN sessions during initialization. Experienced individuals can incorporate access controls to restrict non-VPN traffic. Periodically audit logs to identify irregularities and patch your VPN tool to fix weaknesses.
Protecting Handheld Gadgets with VPNs on Google’s OS and iOS
Phones and tablets are frequent prey for data breaches due to their constant connectivity. Download your VPN app from the Apple App Store to avoid copyright tools. Launch the app, sign in, and choose a server close to your region for quicker response times.
Activate features like malware filtering to improve your internet usage. Set up the VPN to instantly join when accessing open hotspots. For iPhone owners, turn on Always-On VPN in device settings to keep encryption even if the app terminates.
Advanced VPN Features to Boost Your Protection
Today’s services here deliver cutting-edge options that go beyond basic encryption. A network blocker terminates all internet traffic if the VPN drops, avoiding breaches. Server chaining directs your connection through two or more locations, obscuring your online path to a greater extent.
Ad and malware blockers eliminate annoying pop-ups and prevent risky domains. Split tunneling lets you choose which apps use the VPN, optimizing performance and security. For businesses, fixed locations and access permissions simplify protected teamwork.
Addressing Common False Beliefs About VPNs
Despite their popularity, many users misunderstand how VPNs work. A common fallacy is that VPNs completely anonymize your digital behavior. While they mask your IP address, other identifiers can still reveal your identity. Moreover, not all VPNs practice privacy-first principles, so investigating your provider’s policies is essential.
A further misconception is that VPNs severely limit connection rates. While data scrambling adds latency, high-quality providers lessen this impact with high-speed networks. Lastly, no-cost services often compromise security by selling user data or showing targeted advertisements.
Future-Proofing Your Online Presence with a VPN
As technology evolves, remaining secure requires forward-thinking steps. New developments like next-gen processing could threaten current protection methods, making it vital to choose VPNs committed to upgrading their networks. Combining a VPN with supplementary measures like secure storage and biometric checks creates a robust defense framework.
Governments worldwide are strengthening online protection statutes, and a VPN ensures you adhere with these requirements. Whether you’re streaming content, engaging in eSports, or handling professional tasks, a VPN stays an crucial tool for operating the online realm safely.
 Scott Baio Then & Now!
Scott Baio Then & Now! Jenna Von Oy Then & Now!
Jenna Von Oy Then & Now!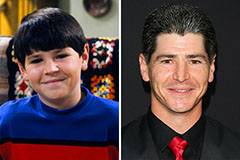 Michael Fishman Then & Now!
Michael Fishman Then & Now! Barry Watson Then & Now!
Barry Watson Then & Now! Burke Ramsey Then & Now!
Burke Ramsey Then & Now!